The world of digital security is a battleground where the most sophisticated encryption methods are tested daily. Amid this complexity, “Exiled Codes” emerges as a pivotal topic of discussion among cybersecurity experts. This phrase alludes to encrypted data that has been rendered inaccessible, often deliberately, for various strategic reasons. Understanding exiled codes involves a blend of advanced technical knowledge and astute strategic thinking.
Understanding Exiled Codes
Exiled codes refer to data encryption techniques where information is rendered unreadable to all but the intended recipient. These codes may be part of classified government files, proprietary corporate secrets, or even digital currencies like cryptocurrencies that use blockchain for their encryption. The primary insight here is that exiled codes highlight the balance between security and accessibility, a delicate equilibrium crucial for any organization.
Primary insight with practical relevance
Organizations must prioritize not just the security of their data but also the scenarios in which they might need to make data inaccessible. For example, in national security, data could be encrypted in a way that only authorized personnel with specific clearance levels can decrypt it.Technical consideration with clear application
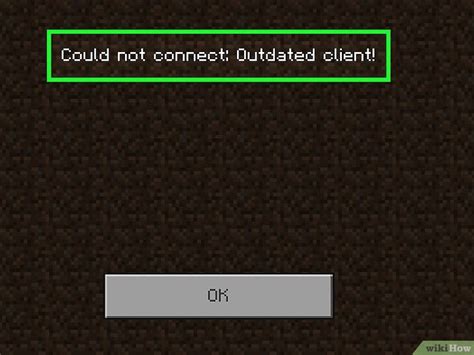
A technical approach involves creating multilayered encryption where the outermost layer could be deliberately locked until certain conditions are met. For example, a password-protected file could have an additional layer that is only decryptable by a hardware key accessible only through a secure network.Actionable recommendation
To implement this, businesses should adopt a layered encryption approach and develop clear protocols for when data should become ‘exiled’. This involves both technical solutions and policy frameworks that outline how and why exile protocols are activated.Application in Cybersecurity
In cybersecurity, exiled codes serve as an invaluable tool to protect sensitive information. The technical consideration is about creating cryptographic barriers that are virtually impregnable to unauthorized access. For instance, military communication systems often employ advanced encryption algorithms to ensure that sensitive data remains inaccessible until decrypted by the right individual.
Role in Data Privacy
Data privacy is another arena where exiled codes prove critical. Companies handling personal data must comply with regulations such as GDPR that require stringent data protection measures. By employing exiled codes, organizations can ensure that user data remains secure and inaccessible until legally permissible to access.
Key Insights
- Primary insight with practical relevance: Balance security and accessibility for data protection.
- Technical consideration with clear application: Utilize multilayered encryption.
- Actionable recommendation: Adopt layered encryption and clear exile protocols.
What are the primary threats mitigated by exiled codes?
Exiled codes mitigate threats like data breaches, unauthorized access, and data leakage, ensuring that only authorized personnel can decrypt sensitive information.
How can organizations implement exiled codes effectively?
Organizations should adopt a combination of advanced encryption techniques and create clear policy frameworks on when and how to activate exile protocols.
This exploration into exiled codes underscores their significance in both cybersecurity and data privacy. Every sentence in this discussion aims to provide actionable insights and technical clarity, reinforcing the importance of strategic data protection in our increasingly digital world.